This month’s $285 million make use of on Drift, a decentralized exchange (DEX), was the biggest crypto hack in over a year, when exchange Bybit lost $1.4 billion. North Korean state-backed hackers were called as prime suspects in both attacks.
This previous fall, assailants impersonated a quantitative trading company and approached Drift’s procedure group face to face at a significant crypto conference, stated Drift in an X post Sunday.
” It is now comprehended that this seems a targeted technique, where people from this group continued to intentionally look for and engage particular Drift factors, face to face, at numerous significant market conferences in numerous nations over the following 6 months,” stated the DEX.
Previously, North Korean cyber spies have actually targeted crypto companies online, through virtual calls and remote work. An in-person technique at a conference would not usually raise suspicion, however the Drift make use of ought to suffice for participants to evaluate connections made at current occasions.
North Korea broadens crypto playbook beyond hacks
Blockchain forensics firm TRM Labs explained the occurrence as the biggest DeFi hack of 2026 (up until now) and the second-largest make use of in Solana’s history, simply behind the $326 million Wormhole bridge hack in 2022.
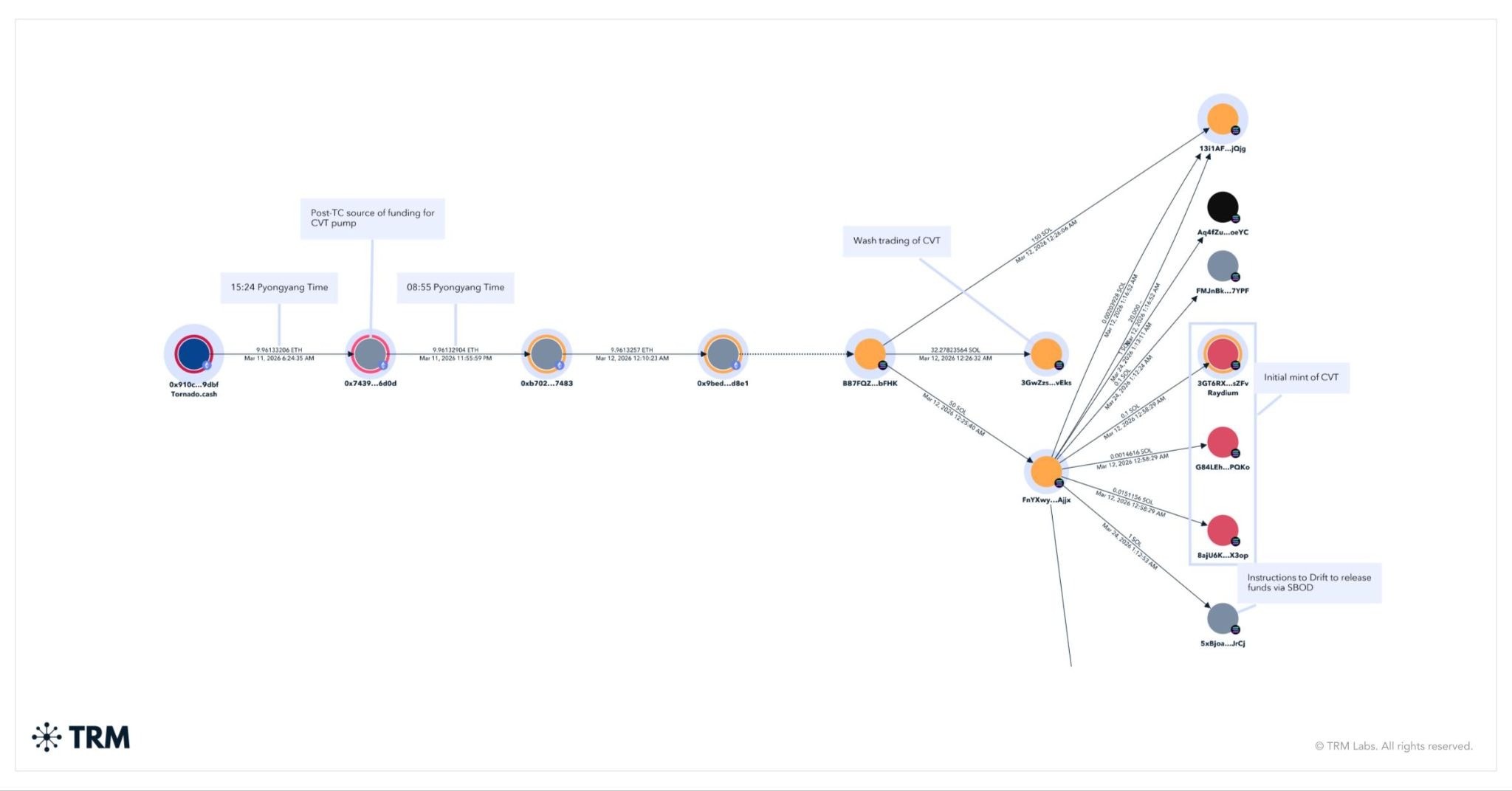
The preliminary contact go back about 6 months, however the exploit itself traces to mid-March, according to TRM. The opponent started by moving funds from Twister Money and releasing the CarbonVote Token (CVT), while utilizing social engineering to convince multisig signers to authorize deals that approved raised approvals.
They then made trustworthiness for CVT by minting a big supply and pumping up trading activity to replicate genuine need. Wander’s oracles got the signal and dealt with the token as a genuine possession.
When the pre-approved deals were performed on April 1, CVT was accepted as security, withdrawal limitations were increased and funds were withdrawn in genuine possessions, consisting of USDC.
Related: North Korean spy mistakes, exposes incorporate phony task interview
According to TRM, the speed and aggressiveness of the subsequent laundering went beyond that seen in the Bybit hack.
North Korea is extensively thought to be utilizing massive crypto thefts such as the Drift and Bybit attacks along with longer-term methods, consisting of putting operatives in remote functions at tech and crypto companies to create consistent earnings. The United Nations Security Council has stated such funds are utilized to support the nation’s weapons program.
Security scientist Taylor Monahan stated seepage of DeFi procedures go back to “DeFi summer season,” including that around 40 procedures have actually had contact with believed DPRK operatives.
North Korean state media reported Thursday that the nation checked an electro-magnetic weapon and a short-range ballistic rocket, called the Hwasong-11, fitted with cluster munition warheads.
Seepage network fuels consistent crypto profits
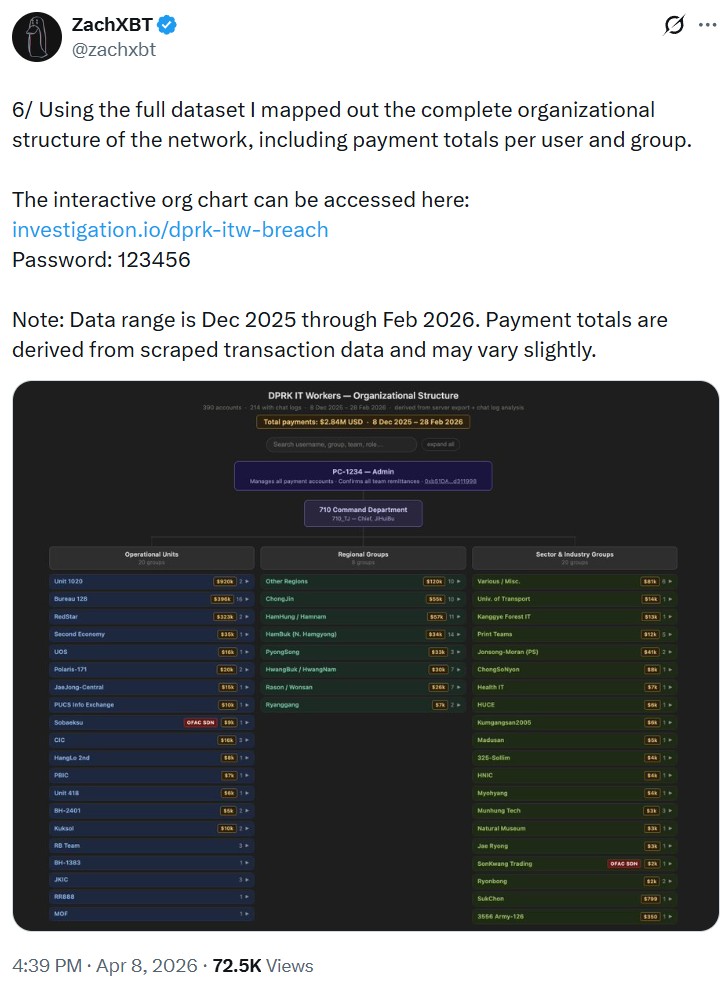
A different examination exposed how a network of North Korea-linked IT employees produced millions through extended seepage.
Information acquired from a confidential source shared by ZachXBT revealed the network impersonating designers and embedding themselves throughout crypto and tech companies, producing approximately $1 million a month and more than $3.5 million considering that November.
The group protected tasks utilizing falsified identities, routed payments through a shared system, then transformed funds to fiat and sent them to Chinese checking account by means of platforms such as Payoneer.
Related: Are you a freelancer? North Korean spies might be utilizing you
The operation depended on fundamental facilities, consisting of a shared site with a typical password and internal leaderboards tracking profits.
The representatives gotten functions in plain sight utilizing VPNs and produced files, indicating a longer-term technique of embedding operatives to draw out consistent profits.
Defenses progress as seepage methods spread out
Cointelegraph experienced a comparable plan in a 2025 examination led by Heiner García, who invested months in contact with a believed operative.
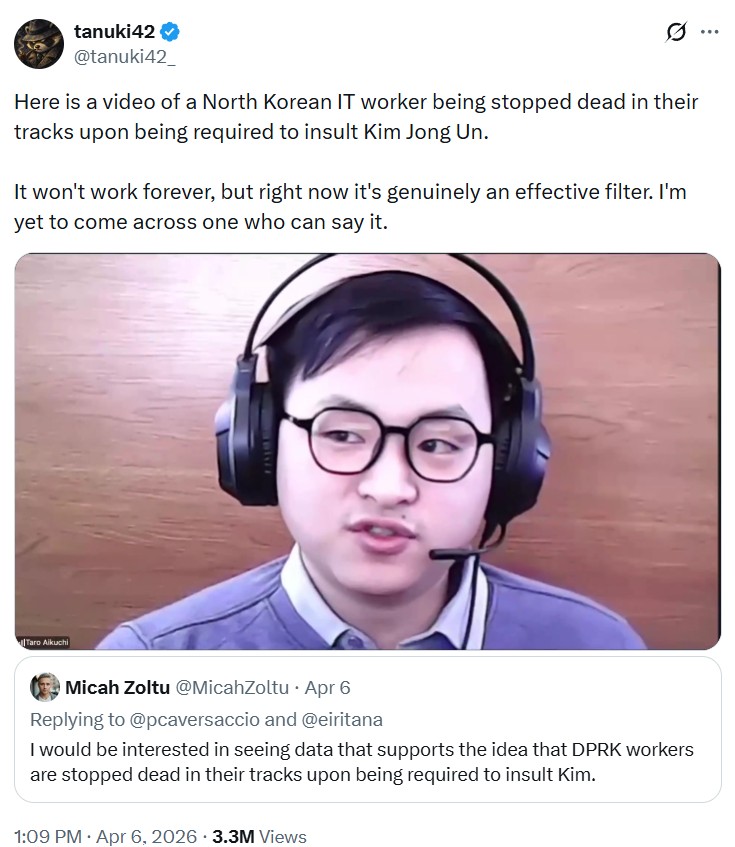
Cointelegraph later on participated in García’s dummy interview with a suspect who passed “Motoki,” who declared to be Japanese. The suspect rage gave up the call after stopping working to present himself in his expected native dialect.
The examination discovered operatives bypassed geographical constraints by utilizing remote access to gadgets physically situated in nations such as the United States. Rather of VPNs, they ran those makers straight, making their activity appear regional.
By now, tech headhunters have actually recognized that the individual at the other end of a virtual task interview might certainly be a North Korean cyber spy. A viral defence technique is to ask suspects to insult Kim Jong Un. Up until now, the method has actually worked.
Nevertheless, as Drift was approached face to face and García’s findings revealed operatives discovering innovative approaches to bypass geographical constraints, North Korean stars have actually continued to adjust to the cat-and-mouse dynamic.
Asking for interviewees to call North Korea’s supreme leader a “fat pig” is an efficient technique for the time being, however security scientists alert that this will not work permanently.
Publication: Phantom Bitcoin checks, China tracks tax on blockchain: Asia Express


